Introducing Istio Ambient Mesh
By Idit Levine, Founder/CEO Solo.io
New Choices for the Istio CommunitySolo.io and Google recently contributed a significant new architecture to the Istio project, called Istio Ambient Mesh..

This contribution is the culmination of nearly a year of engineering effort that began within Solo.io, and merged together with Google engineering as we discovered that we were both working towards similar goals for Istio. Now that the code is available to the Istio community, we’re excited to see how this new architectural option for the Istio data plane evolves.
What is Ambient Mesh?
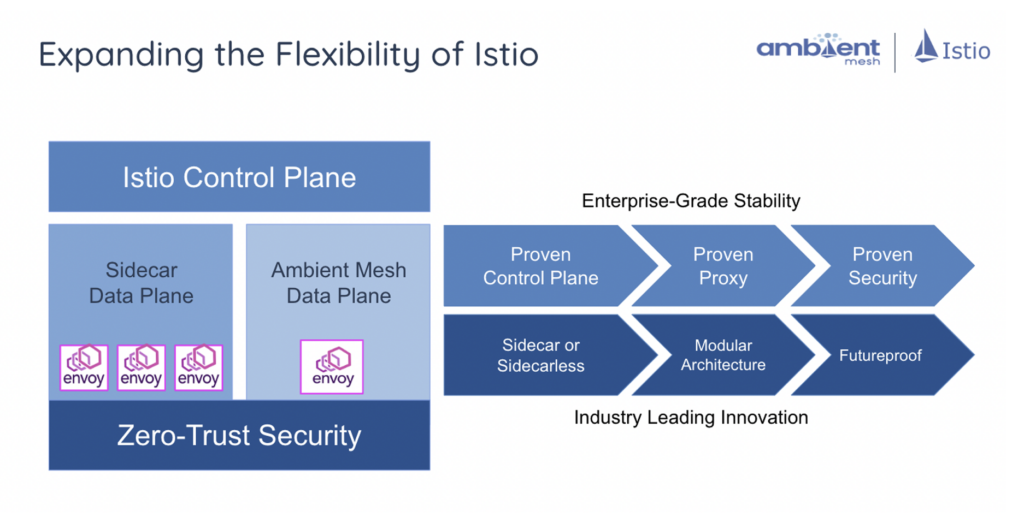
Istio Ambient Mesh builds on 5+ years of experience in the Istio community, with thousands of production deployments and contributions from neary 1000 engineers. It also builds on the proven security model of Istio.
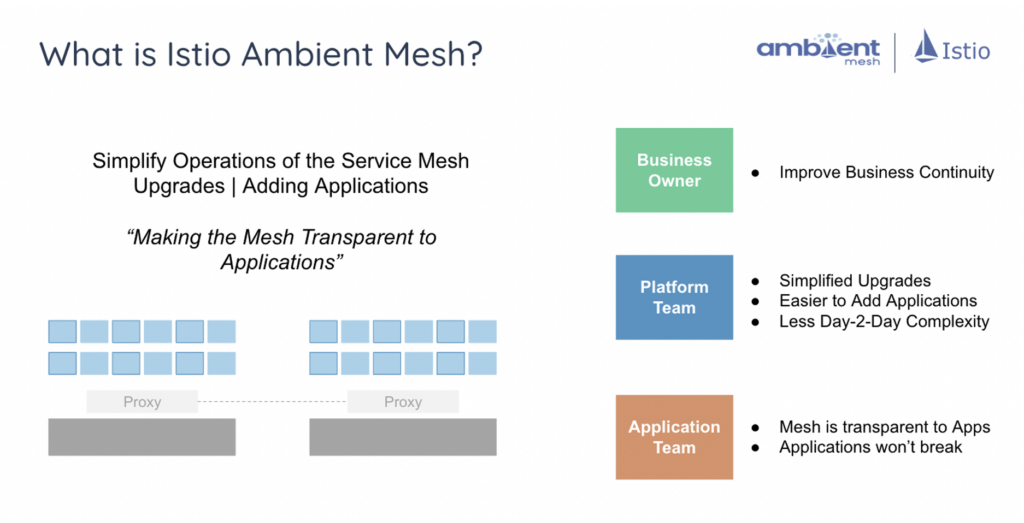
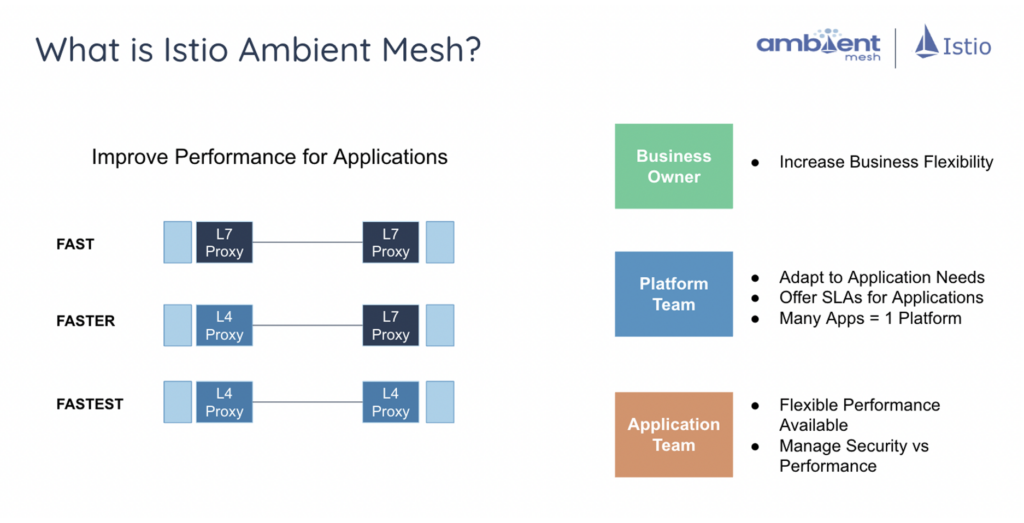
Istio Ambient Mesh is the new Istio dataplane architectural alternative that does not rely on sidecars by default. Istio Ambient Mesh allows customers to have choices around the vectors of cost, operational transparency, and performance.
Istio Ambient Mesh enables Istio to deliver value to our Gloo Mesh customers in the following areas:
- All Istio technology is open source and backed by more than five years of ongoing development, stabilization, and innovation – trusted, and future-proofed
- Operational transparency choices for Proxy technologies – data plane runs outside applications for simple application onboarding, upgrading, and CVE patching
- Cost optimization choices for Proxy technology – customers can more finely align the cost of operational and compute resources for “right size” usage
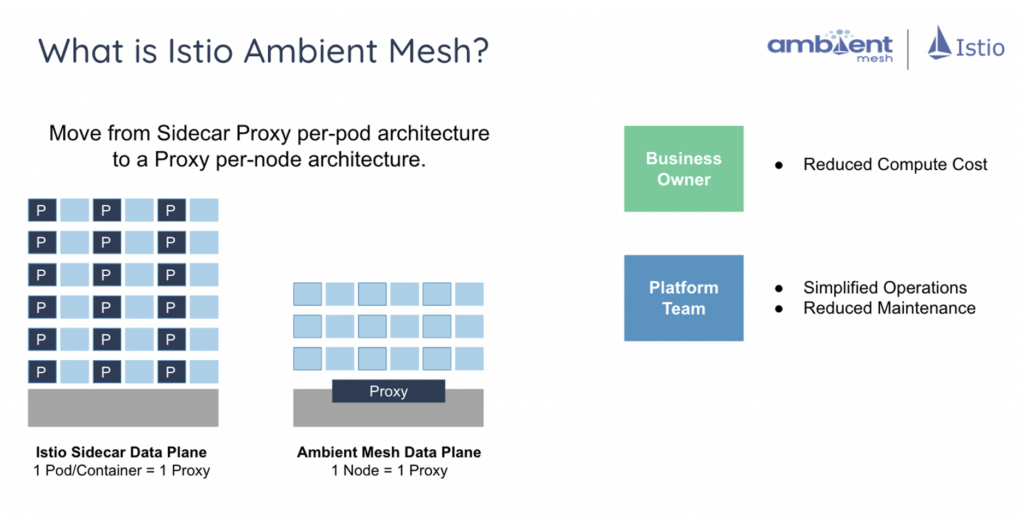
- Flexible choice of sidecar (standard Istio architecture) or sidecar-less (Istio Ambient Mesh architecture, which can be mixed or matched to be aligned to customer’s application needs – customers can match the best setting to their application needs.
- Performance optimization choices for how Layer 4 or Layer 7 services are deployed – customers will get great performance in all configurations.
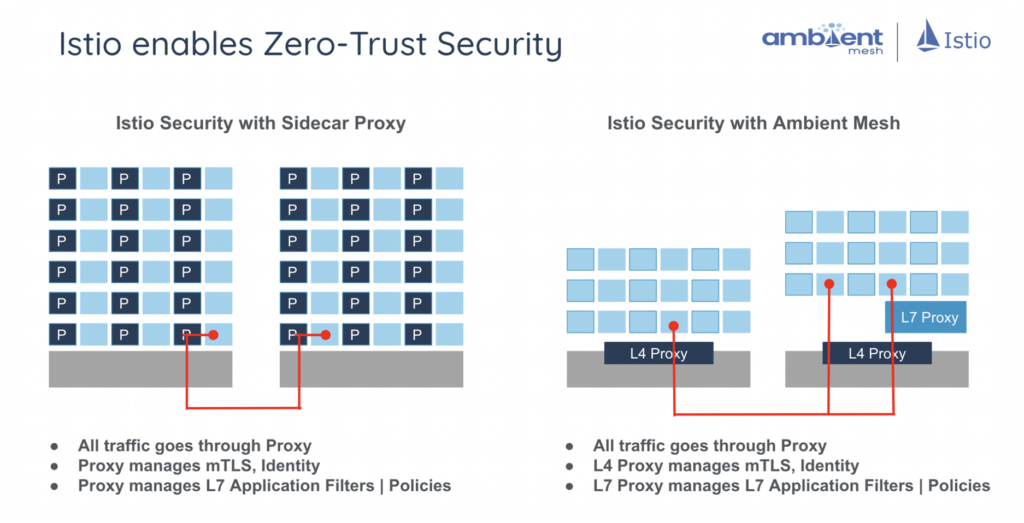
- Separation of application code from data plane gives a better security posture
Customer Choice, without Security Compromises
Istio has always had Zero-Trust Security built in and enabled by default. By enabling cryptographically-generated identity, Zero-Trust Security is never compromised with either sidecar or sidecar-less architectures. Security is never a tradeoff that customers need to worry about. What we’ve learned over time is that service mesh deployments involve multiple groups (CloudOps, DevOps, SRE)
The Featured Blog Posts series will highlight posts from partners and members of the All Things Open community leading up to the conference in the fall.
